In cybersecurity, we're trained to identify threats and neutralize them with precision. But when it comes to leadership, the biggest threat is often invisible: our own unconscious biases, reactive patterns, and the illusion that spreadsheets alone can guide us through complex human situations.
I learned this the hard way. Early in my career, I was that leader who believed every decision could be optimized through data analysis. If the metrics said yes, we moved forward. If they said no, we stopped. It felt clean, objective, bulletproof.
Then I had to let someone go that I genuinely cared about.
When Data Meets Humanity
The numbers were clear: performance metrics were declining, project deadlines were being missed, and team productivity was suffering. By every measurable standard, the decision was obvious. But something didn't sit right with me.
Instead of acting immediately on the data, I paused. I asked myself what my gut was telling me and, more importantly, what my values demanded of me as a leader.
That pause changed everything.
I discovered this person was struggling with a family crisis they hadn't felt safe enough to share. The "performance issues" were actually symptoms of someone drowning who needed support, not judgment. We restructured their responsibilities temporarily, connected them with resources, and six months later they became one of our strongest contributors.
The data told me to cut them loose. My intuition sensed there was more to the story. My values demanded I dig deeper. Conscious decision-making meant integrating all three.
Beyond "Gut" vs. "Spreadsheet" Leadership
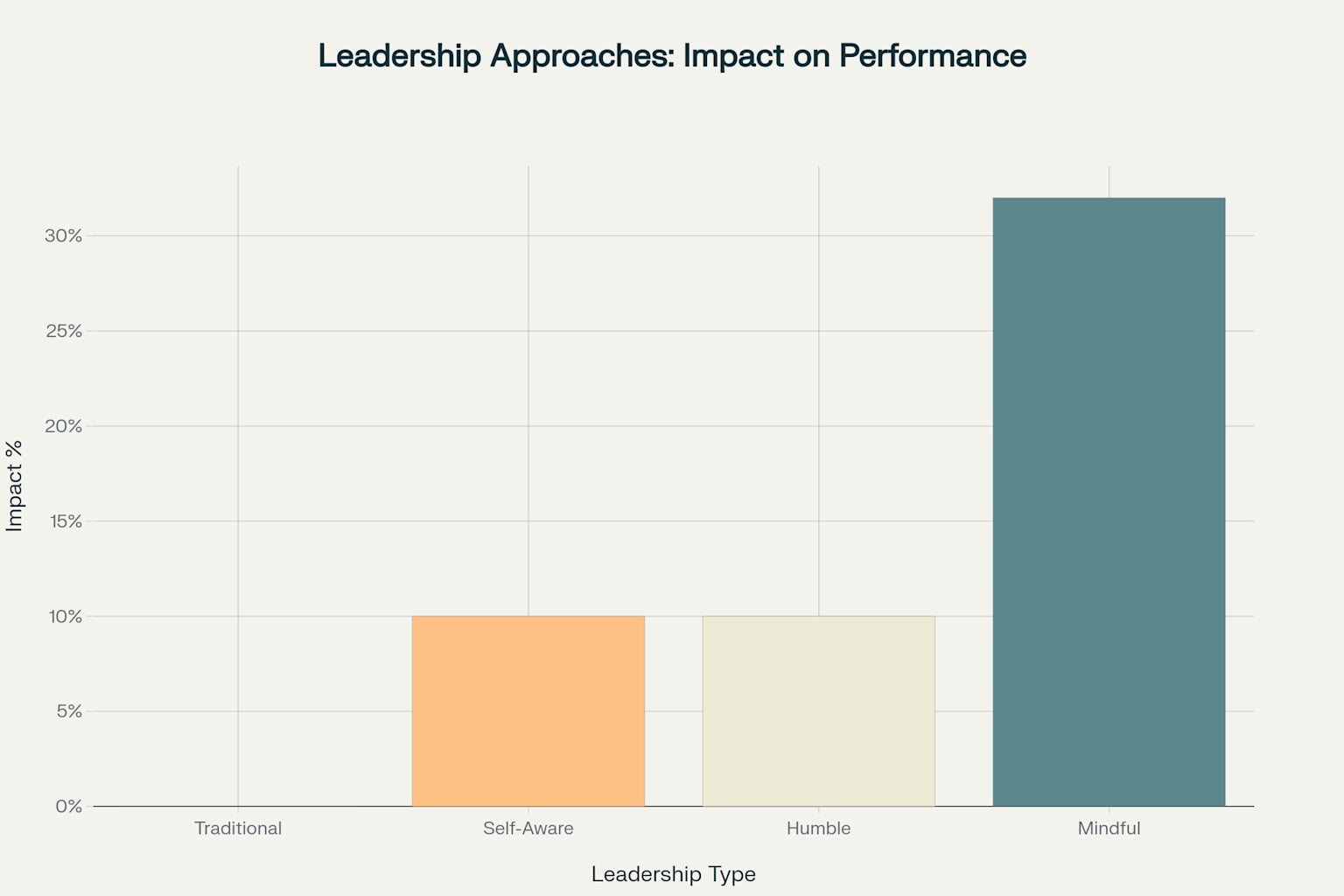
Most leaders fall into one of two camps: the analytical types who worship at the altar of data, or the instinctive leaders who trust their gut above all else. Both approaches are incomplete and potentially dangerous.
Data-driven leaders make consistent, defensible decisions but often miss the human nuances that spreadsheets can't capture. They risk becoming so focused on metrics that they forget they're leading people, not numbers.
Gut-driven leaders can pivot quickly and connect with their teams emotionally, but they're vulnerable to cognitive biases and blind spots. Their decisions may feel right in the moment but lack the rigor needed for complex organizational challenges.
Conscious leaders understand that the most effective decisions emerge from the integration of analytical insights, intuitive wisdom, and core values. This isn't about finding balance; it's about creating synthesis.
The Three Pillars of Conscious Decision-Making
Pillar 1: Data as Foundation, Not Dictator
Data provides the foundation for understanding what's happening, but it can't tell you what it means or what you should do about it. In cybersecurity, we see this constantly. A spike in failed login attempts is just a number until human judgment determines whether it's a targeted attack or a legitimate user having a bad day with their password.
The key is to use data to inform, not replace, human judgment. Start with the facts, but don't end there.
Pillar 2: Intuition as Internal Compass
Your intuition isn't mystical; it's your brain processing thousands of subtle cues too quickly for conscious analysis. It's pattern recognition honed by experience, emotional intelligence reading the room, and your unconscious mind connecting dots that logical analysis might miss.
But intuition requires calibration. The most dangerous leaders are those who confuse ego with intuition, or bias with insight. Conscious leaders learn to distinguish between authentic intuitive wisdom and reactive emotional patterns.
Pillar 3: Values as True North
Your values aren't just nice words on a website; they're your decision-making criteria when the stakes are highest. They answer the question: "Even if we could do this, should we?"
Values-based decision-making doesn't mean being soft or impractical. It means being clear about what kind of leader and organization you want to be when the pressure is on.
A Framework for Integration
When facing a significant decision, I now use what I call the IVLD Framework:
Interrogate the Data: What story do the metrics tell? What don't they tell? What additional data do I need?
Validate with Values: Does this align with who we say we are? Would I be proud of this decision in five years?
Listen to Intuition: What feels right? What feels off? What am I not seeing?
Decide with Integration: How do these three perspectives inform each other? Where do they conflict, and what does that tension reveal?
This isn't a linear process. Sometimes intuition points you toward data you hadn't considered. Sometimes values clarify why the "obvious" choice feels wrong. Sometimes data reveals that your gut reaction is based on outdated assumptions.
The Cost of Unconscious Leadership
Leaders who operate unconsciously, making decisions based on reactive patterns rather than conscious integration, create predictable problems:
Analysis paralysis when faced with ambiguous situations that don't fit neat categories.
Empathy deficit in their teams because people don't feel seen or understood beyond their performance metrics.
Cultural toxicity because values become empty words rather than lived principles.
Strategic blind spots because they're not leveraging their full decision-making capacity.
The cybersecurity field is particularly vulnerable to these patterns because our technical experience and training emphasizes binary thinking: secure or vulnerable, compliant or non-compliant, threat or no threat. But leadership requires nuanced thinking about complex human systems.
Self-Mastery: The Inner Work of Leadership
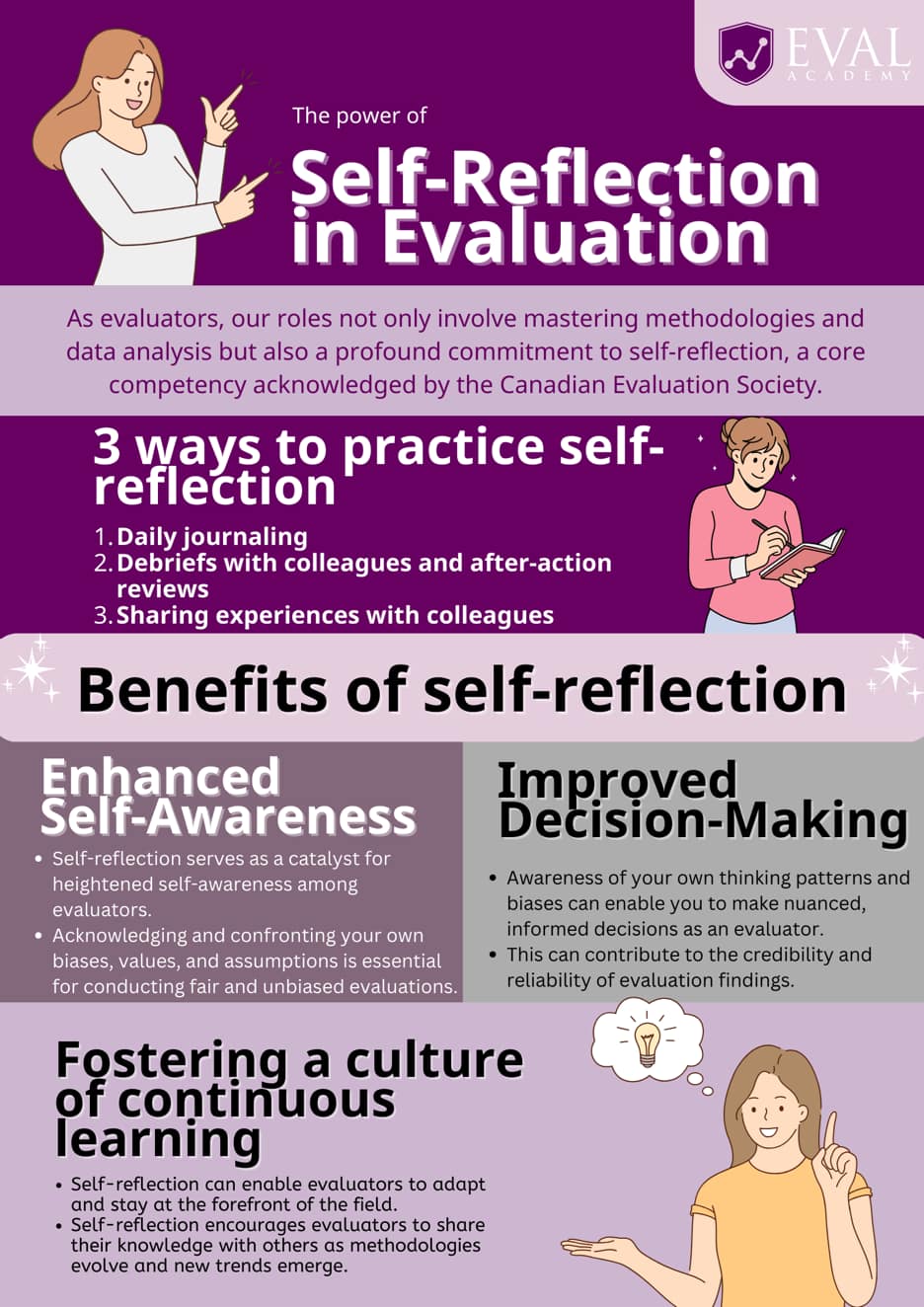
Conscious decision-making starts with self-mastery. You can't integrate intuition, data, and values if you don't know yourself well enough to distinguish between them.
This means doing the uncomfortable work of examining your biases, triggers, and blind spots. It means getting comfortable with not having all the answers immediately. It means building the emotional intelligence to read not just the data, but the room.
The most effective leaders I know aren't the smartest or the most charismatic. They're the most self-aware.
They know their strengths and compensate for their weaknesses. They can separate their ego from their decision-making. They create psychological safety for their teams to challenge their thinking and provide input they might not want to hear.
Making Better Decisions Under Pressure
The real test of conscious leadership isn't in the comfortable moments when you have time to analyze every angle. It's when the stakes are high, information is incomplete, and everyone is looking to you for direction.
This is where the integration of intuition, data, and values becomes most crucial. Your unconscious competence, built through years of experience and reflection, allows you to make sound decisions quickly without abandoning your principles or ignoring available information.
But this capability isn't automatic. It requires practice, feedback, and continuous refinement of your decision-making process.
The Ripple Effect
When leaders make decisions consciously, integrating multiple ways of knowing, something profound happens in their organizations. Teams begin to trust not just the leader's competence, but their judgment. People feel valued as whole human beings, not just resources to be optimized.
Innovation increases because diverse perspectives are welcomed rather than seen as obstacles to efficiency. Resilience grows because the organization isn't dependent on any single way of processing information or making decisions.
Most importantly, other leaders begin to model the same approach, creating a culture where conscious decision-making becomes the norm rather than the exception.
Your Next Decision
The next time you're facing a significant decision, try this: Before you dive into the analysis or follow your first instinct, pause. Ask yourself:
- What do I need to know that I don't know yet?
- What is my intuition telling me about this situation?
- How does this decision reflect our stated values?
- What would the person I want to become do in this situation?
Conscious leadership isn't about having all the answers. It's about asking better questions, especially of ourselves. It's about showing up as whole human beings who happen to be in positions of authority, rather than role-playing what we think a leader should look like.
The stakes are too high, and the problems too complex, for anything less than our full decision-making capacity. Our teams, our organizations, and our communities deserve leaders who can think, feel, and choose with both wisdom and courage.
The question isn't whether you'll face difficult decisions. The question is whether you'll face them consciously.
#
References
- Conscious Leadership: Leading with Awareness and Integrity. California Institute of Integral Studies. (2024). https://www.ciis.edu/news/conscious-leadership-transforming-leadership-awareness-and-integrity
- Decision-Making Skills: Balancing Intuition and Data in Making Informed Decisions. LinkedIn. (2024). https://www.linkedin.com/pulse/decision-making-skills-balancing-intuition-data-making-informed-h3yse
- Bahshwan, A.F. (2024). The Role of Emotional Intelligence in Effective Leadership. International Journal of Engineering Research and Technology, 13(5). DOI: 10.17577/IJERTV13IS050283
- Forbes Coaches Council. (2022). Why Developing Conscious Leadership Is Essential To Future Shaping. Forbes. https://www.forbes.com/councils/forbescoachescouncil/2022/08/01/why-developing-conscious-leadership-is-essential-to-future-shaping/
- Kaplan, S. (2024). Data-Driven Decision Making vs. Intuition-Based Leadership. Soren Kaplan. https://www.sorenkaplan.com/middle-ground-data-driven-decision-making-vs-intuition-based-leadership/
- Dooshima, K.V. (2024). The Role of Emotional Intelligence in Effective Leadership and Its Impact on Team Performance: A Study of the University of Ibadan, Nigeria. International Journal of Business and Management Review, 12(2), 75-138.
- AACSB. (2024). The Practice of Conscious Leadership. AACSB Insights. https://www.aacsb.edu/insights/articles/2024/06/the-practice-of-conscious-leadership
- Entrepreneur. (2024). How to Blend Data and Intuition for Better Decision-Making. https://www.entrepreneur.com/leadership/how-to-blend-data-and-intuition-for-better-decision-making/475914
- Baldry, D. (2022). Values-Based Decision Making: The Benefits and Challenges Associated with Driving a Set of Organizational Values. International Journal of Co-operative Accounting and Management, 5(1). DOI: 10.36830/IJCAM.20225
- The Industry Leaders. (2024). Leadership Effectiveness Linked to Growing Focus on Self-Awareness. https://www.theindustryleaders.org/post/leadership-effectiveness-linked-to-growing-focus-on-self-awareness
- LinkedIn. (2023). The Leadership Paradox: Intuition Versus Data-Driven Decisions. https://www.linkedin.com/pulse/leadership-paradox-intuition-versus-data-driven-nandhagopal-qiw8c
- Schnelle, D., et al. (2023). Values, decision-making and empirical bioethics: a conceptual model for empirically identifying and analyzing value judgements. Theoretical Medicine and Bioethics, 44(6), 567-587. DOI: 10.1007/s11017-023-09640-4
- INTOO. (2024). How Self-Awareness Enhances Leadership Effectiveness. https://www.intoo.com/us/blog/how-self-awareness-enhances-leadership-effectiveness/
- Forbes Coaches Council. (2024). How To Balance Data-Driven Decision-Making And Intuitive Leadership. Forbes. https://www.forbes.com/councils/forbescoachescouncil/2024/08/30/how-to-balance-data-driven-decision-making-and-intuitive-leadership/
- Mattone, J. (2025). The Role of Self-Awareness in Leadership: How Knowing Yourself Leads to Success. John Mattone Global. https://johnmattone.com/blog/the-role-of-self-awareness-in-leadership-how-knowing-yourself-leads-to-success/
- Harvard Business Review. (2025). Data and Intuition: Good Decisions Need Both. https://www.harvardbusiness.org/data-and-intuition-good-decisions-need-both/
- McKinsey & Company. (2021). Psychological safety and the critical role of leadership development. https://www.mckinsey.com/capabilities/people-and-organizational-performance/our-insights/psychological-safety-and-the-critical-role-of-leadership-development
- ASCD. (2025). How Can Leaders Overcome Cognitive Bias? https://www.ascd.org/el/articles/how-can-leaders-overcome-cognitive-bias
- Venables, P. (2021). Cybersecurity and the Curse of Binary Thinking. https://www.philvenables.com/post/cybersecurity-and-the-curse-of-binary-thinking
- Center for Creative Leadership. (2025). How Leaders Can Build Psychological Safety at Work. https://www.ccl.org/articles/leading-effectively-articles/what-is-psychological-safety-at-work/
- Fiveable. (2024). Leadership Cognitive Biases. Business Cognitive Bias Class Notes. https://library.fiveable.me/cognitive-bias-in-business-decision-making/unit-10
- Porup, J.M. (2024). Binary Thinking is Bad. Cyber Cyber Cyber Cyber Newsletter. https://ninja.cybercybercybercyber.ninja/p/binary-thinking-is-bad
- Westford. (2024). The Psychology of Decision-Making: Overcoming Bias in Leadership. https://westfordforbusiness.com/the-psychology-of-decision-making-overcoming-bias-in-leadership/
- Snowden, D. & Boone, M. A Leader's Framework for Decision Making. Harvard Business Review. Systems Wisdom. https://www.systemswisdom.com/sites/default/files/Snowdon-and-Boone-A-Leader's-Framework-for-Decision-Making_0.pdf
- Link Centre. (2024). Beyond Conscious Leadership: The Key Role of the Unconscious Mind. https://www.linkcentre.com/news/beyond-conscious-leadership-the-key-role-of-the-unconscious-mind/
- InfoPro Learning. (2023). Unlocking Effective Leadership with Emotional Intelligence Training. https://www.infoprolearning.com/blog/emotional-intelligence-in-leadership-strategies-for-developing-eq-through-training/
- Symbio. (2023). The Art of Choice: 35 Decision-Making Frameworks. https://symbio6.nl/en/blog/decision-making-framework
- Acquire Global Coaching. (2024). Unleashing Unconscious Competence in Leadership. https://www.acquirecoaching.com/insights/unleashing-unconscious-competence-in-leadership-insights-from-jass-malaney-professional-executive-coach
- Harvard Division of Continuing Education. (2025). Emotional Intelligence in Leadership Training Program. https://professional.dce.harvard.edu/programs/emotional-intelligence-in-leadership/
- Quantive. (2022). A Framework For Leadership Decision-Making. https://quantive.com/resources/articles/leadership-decision-making-guide
- Segal, A. (2018). Great Leaders are Unconsciously Competent: Here's How They Become That Way. LinkedIn. https://www.linkedin.com/pulse/great-leaders-unconsciously-competent-heres-how-become-annette-segal